Report - Cutting the Lines: Hybrid conflict and the battle for global connectivity
July 26, 2025
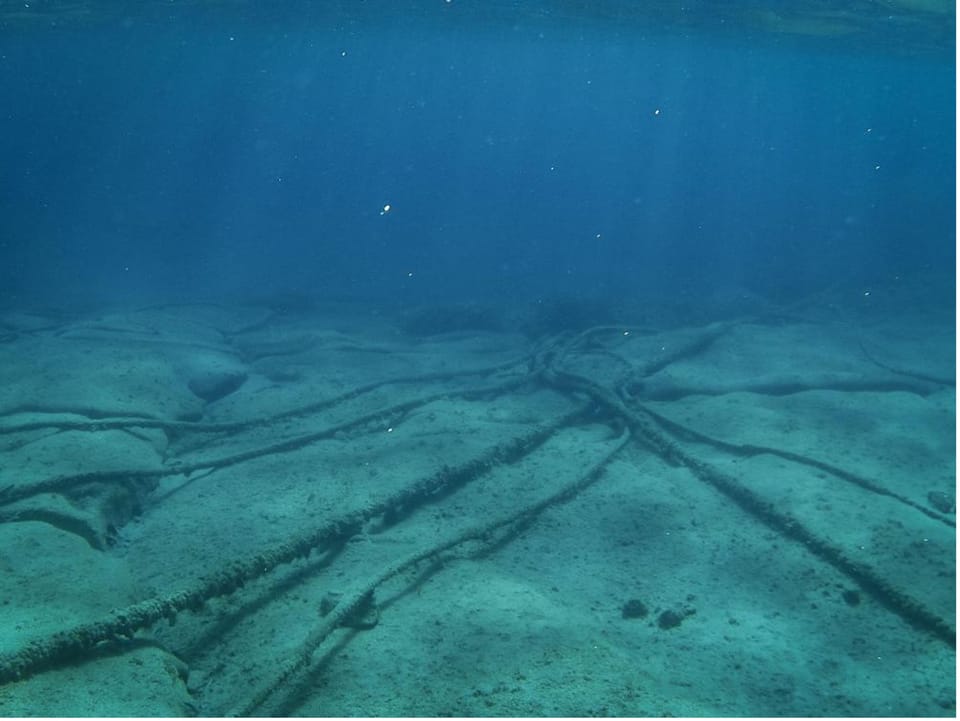
Global connectivity relies on a hidden yet indispensable layer of infrastructure: undersea fiberoptic cables. These cables, which carry more than 99% of intercontinental data traffic, form the backbone of the digital economy and global communications. Every day, over $10 trillion in financial transactions depend on their uninterrupted operation. Yet in recent years, this critical system has faced an alarming rise in disruptions—some accidental, others increasingly suspected to be deliberate.
Across Europe, especially in the Baltic Sea, a dense web of cables and pipelines has become a focal point for suspicious maritime incidents. While some outages stem from routine fishing or anchoring activity, a growing body of evidence suggests coordinated sabotage by state-linked actors, masked as normal maritime operations. These patterns signal a shift toward hybrid tactics—where physical infrastructure is quietly targeted below the threshold of open conflict. Intelligence agencies, NATO, and regional governments have taken notice, but institutional responses remain fragmented.
In parallel, the Asia-Pacific—home to one of the world’s most concentrated submarine cable networks—faces its own vulnerabilities. Slow repair times, regulatory bottlenecks, and limited maintenance capacity have created a dangerous gap between infrastructure growth and operational resilience. Some island nations, like Tonga or Taiwan’s Matsu Islands, have endured prolonged outages with major economic and security consequences. As geopolitical rivalries intensify, concerns over ownership, access, and sabotage risks are driving new alignments and infrastructure strategies.
Meanwhile, the global financial sector—the most data-dependent industry of all—remains critically underprepared. While there are playbooks for cyberattacks and financial crises, no equivalent framework exists for managing extended cable outages. Market volatility, transactional delays, and systemic risks loom large if multiple disruptions occur simultaneously.
This report analyzes the escalating risks to undersea infrastructure through a regional and sectoral lens. It maps the technical, political, and economic fault lines emerging across Europe and the Indo-Pacific, highlights the strategic motivations behind suspected sabotage, and assesses the readiness of financial and regulatory institutions. As cables become contested terrain in both geopolitical and economic terms, strengthening their resilience must become a global priority—before the next outage triggers a crisis that can no longer be dismissed as hypothetical.
The Seabed Front: strategic disruption in the Age of submarine cable warfare
What was once the exclusive domain of 19th-century naval warfare — severing undersea cables to disrupt an enemy’s communication — has re-emerged in the 21st century as a sophisticated, high-stakes theater of hybrid conflict. The methods may be less dramatic than hacksaws in stormy waters, but the strategic effect is far greater. The world now relies on a vast web of undersea cables that carry 99% of all international telecommunications: phone calls, financial transactions, military data, and global internet traffic. There are more than 530 of these submarine cable systems in service, spanning over 850,000 miles. And their vulnerability is rapidly becoming a point of geopolitical leverage.
The global subsea cable network, though robust in volume, is fragile by design. These cables, often no thicker than a garden hose, are laid in deep waters with minimal protection. In shallow coastal zones — where most disruptions occur — they are armored, but even then, they can be severed with a ship’s anchor or fishing gear. According to data from Recorded Future, more than 100 cable faults occur each year. Most are accidental. But the operational techniques used for accidental damage are also the same ones available to hostile actors. The difference lies in intent — and intent, in this domain, is rarely declared.
State-sponsored operations have likely already tested this logic. Russia, which has long maintained a capability for deep-sea reconnaissance and sabotage, has been observed mapping cable routes and operating submarines aggressively near key junctions from the North Sea to northeast Asia. U.S. and NATO sources have for years assessed Russia’s willingness to target the undersea network, particularly in retaliation for Western support to Ukraine. Chinese activity is equally concerning, albeit more subtle. In Taiwan’s case, state-linked vessels — fishing boats, dredgers, and cargo ships — have caused cable damage dozens of times in recent years. The disruption of links to Taiwan’s Matsu Islands in early 2023 was described by one analyst as a “dry run for an invisible blockade.”
The threat is not only from sabotage, but also surveillance. Cables are vulnerable not just to cutting but to tapping. The Snowden revelations made clear that Western intelligence agencies have long used undersea cables as surveillance conduits. Today, China is seeking greater ownership of the global cable infrastructure through state-backed firms, raising concerns in Washington and Brussels that the infrastructure itself may become a vector for interference, surveillance, or geopolitical influence.
This context explains why even one-off incidents — like the Baltic Sea cable cuts in November 2024 — are taken seriously. The strategic messaging is potent, even when the operational impact is limited. These actions communicate capability and intent, and they force governments to acknowledge their exposure. As experts have noted, deliberate cable attacks don’t need to be continuous to be effective. Their strength lies in ambiguity. The ability to strike, and to be credibly suspected of striking, is enough to destabilize. The economic implications are no less severe. Submarine cables cost tens of thousands of dollars per mile, with major systems like transatlantic routes priced in the hundreds of millions. Repairs are slow, complex, and rely on a small pool of specialized ships. In wartime scenarios, disruption could sever military command systems, paralyze financial markets, and isolate entire regions. Even short-term outages, if sustained or repeated, could cascade into broader systemic failures.
From a defense perspective, the challenge is immense. Protecting thousands of miles of submerged, lightly armored infrastructure across international waters — most of it privately owned — requires a shift in both mindset and capability. It is not just a naval issue, but one that spans cyber defense, supply chain resilience, intelligence sharing, and civilian-military coordination. The actors threatening this infrastructure do not need to dominate the seas. They need only to exploit opacity and hesitation.

What we are witnessing now is a contest for the seabed — a silent, submerged extension of great power competition. It is no longer a theoretical vulnerability. It is an active front.

|
Date |
Location |
Incident |
Suspected Vessel / Actor |
Details / Suspicion Basis |
|
Apr 2021 |
Lofoten-Vesterålen, Norway |
12-ton cable segment ripped out from ocean observatory |
Russian trawler Saami |
Repeated crossings over site, cable cleanly cut |
|
Dec 25, 2024 |
Baltic Sea (Finland–Estonia, Finland–Germany) |
Multiple fiberoptic cables severe |
Eagle S (Russian oil, UAE-owned) |
Changed course post-cable crossing, suspected anchor dragging |
|
Nov 17–18, 2024 |
Lithuania–Gotland & Germany–Finland |
Two cables disabled |
Yi Peng 3 (China-owned)
|
AIS off, anchor damage, slowed near cables |
|
Aug 2024 |
Balticconnector pipeline + 2 cables |
Gas pipeline and nearby cables damaged |
Newnew Polar Bear (Hong Kong-flagged) |
Anchor found near damage; China called it an accident |
|
Late 2021 |
Norway–Svalbard |
Deep-buried cable damaged |
Melkart 5 and Yagry (Russian trawlers) |
Trenching observed; suspicious ship patterns |
|
Mar 2024 |
Red Sea |
Four undersea cables cut |
Unknown |
Disrupted 25% of Asia–Europe internet traffic |
|
Feb 2023 |
Taiwan (Matsu Islands) |
Cables severed, island internet disabled |
Unknown |
14,000 affected; repair took two months |

Europe’s Undersea Infrastructure Under Attack: A Strategic Vulnerability Exposed
Europe is entering a phase of heightened vulnerability in a domain long considered secure by default: its seabed infrastructure. Across the continent — especially in the Baltic and Nordic regions — an emerging pattern has taken shape, marked by the repeated disruption of undersea fiberoptic cables and pipelines. While isolated cable failures have always been part of maritime operations, recent incidents share too many commonalities to be dismissed as coincidence or bad luck. Investigative attention has increasingly turned toward the likelihood of deliberate sabotage carried out under the cover of civilian maritime traffic.
The consistent elements across these cases are difficult to ignore. In nearly all major incidents, there has been the presence of large commercial vessels with ambiguous ownership structures — often operating under flags of convenience — near the failure points. These ships often alter their course unexpectedly, slow down as they approach cable routes, and, in some instances, turn off their AIS tracking systems entirely. Physical evidence gathered in several investigations shows signs of anchor dragging and seabed trenching that suggest intentional action rather than random damage.
Attribution remains complex, and that is precisely the point. The design of these operations favors ambiguity. The use of commercial vessels, plausibly unrelated to any military entity, combined with the difficulty of real-time underwater surveillance, gives state actors the space to operate just beneath the threshold of direct confrontation. The goal appears to be not only to test Europe’s ability to monitor and respond, but also to probe for structural weaknesses and sow uncertainty — both among populations and within decision-making circles.
Though Russia and China are never publicly named in official European statements, they are the implicit subjects of most defense ministry briefings and private-sector threat assessments. The pattern of incidents aligns too well with their strategic interests. For Russia, in particular, disrupting the flow of data and energy across the Baltic could serve several purposes at once: demonstrating asymmetric capability, undermining EU cohesion, retaliating against sanctions, or laying groundwork for contingency operations in a future military scenario. China’s suspected involvement in some cases suggests a shared operational logic: project pressure and uncertainty far from home shores without triggering escalation.
What makes this threat so insidious is the reliance of modern states on the very infrastructure being targeted. Undersea cables are not just technical links — they are the backbone of the global internet, financial markets, and even military command structures. Their physical vulnerability stands in stark contrast to their critical function. And yet, until recently, few states treated their protection as a strategic priority. The oversight and maintenance of these assets remain largely in the hands of private companies. That disconnect between strategic importance and operational responsibility is increasingly untenable.
European governments have begun to respond, but most measures remain reactive. NATO has expanded surveillance missions in the Baltic and North Sea, and new units have been created to map vulnerabilities and promote information sharing.

The UK, among others, has invested in dedicated monitoring vessels. Still, even the most advanced surveillance systems are limited by the scale of the seabed and the stealth of the tactics being used. Intelligence agencies now acknowledge that full deterrence is unlikely; instead, resilience — the ability to restore functionality quickly and operate under disruption — has become the strategic objective.
There is also growing awareness that future cable sabotage may not only be used for disruption, but also for access. Damaging a cable is one way to insert surveillance devices or reroute traffic for monitoring. The same actors suspected of dragging anchors might just as well be collecting data or mapping undersea infrastructure for future operations. The overlap with cyber operations is real and growing.
What emerges is a picture of an evolving threat space where the seabed is becoming a contested domain. The adversaries are not overtly declaring conflict but are instead incrementally shifting the balance of security through ambiguity, pressure, and calculated risk. Europe’s response must reflect that same complexity — blending intelligence coordination, infrastructure hardening, real-time domain awareness, and international cooperation.
If undersea sabotage continues at its current pace and ambiguity remains the norm, it may soon be accepted as a cost of doing business in the modern geopolitical environment — unless the West adapts quickly and clearly signals that these operations will be detected, attributed, and deterred.
|
SEPT 2022 |
NORD STREAM BLASTS |
On September 26, 2022, three of the four Nord Stream 1 and 2 pipelines—built by Russia’s Gazprom to supply gas to Germany—were ruptured by undersea explosions near Denmark’s Bornholm Island, releasing large amounts of methane. Swedish investigators found explosive residues, confirming sabotage, but both Sweden and Denmark closed their probes in 2024 without identifying culprits. Western officials speculated Russia may have sabotaged its own infrastructure, a claim rejected by President Putin. Moscow, in turn, blamed the U.S., UK, and Ukraine—all of whom denied involvement. In August 2024, Germany sought Poland’s help to arrest a Ukrainian diving instructor allegedly linked to the attack, but he had already fled the country. No one has claimed responsibility.
|
|
OCT 2023 |
BALTICCONNECTOR GAS PIPE AND CABLES |
On October 8, 2023, the Balticconnector gas pipeline linking Finland and Estonia was severed, with Finnish investigators identifying the Chinese vessel New Polar Bear as the likely culprit due to anchor dragging. Estonian authorities also suspect the same vessel damaged undersea telecom cables between Estonia, Finland, and Sweden the previous day. Though China pledged cooperation, Estonian officials reported little follow-through. Investigations have yet to conclude whether the incidents were accidental or intentional. The ship, flagged in Hong Kong, was en route to a Russian port near St. Petersburg at the time.
|
|
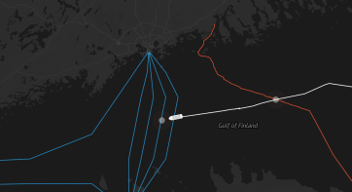
NOV 2024 |
BALTIC TELECOM CABLES |
On November 17–18, 2023, two undersea fiber-optic cables in the Baltic Sea—one linking Lithuania to Sweden’s Gotland and another connecting Finland to Germany—were severed within 24 hours, raising suspicions of sabotage. Investigators from affected countries focused on the Chinese bulk carrier Yi Peng 3, whose route and timestamps matched the cable breach locations. The vessel had departed from Russia’s Ust-Luga port on November 15. Following a diplomatic standoff, China permitted limited onboard access to European investigators on December 21 but denied a Swedish prosecutor the right to conduct a full preliminary investigation.
|
|
DEC 2024 |
POWER AND INTERNET CABLES |
On December 25, 2024, the Estlink 2 undersea power cable between Finland and Estonia, along with four telecom cables, was damaged. Finland launched a sabotage investigation and seized the Eagle S, a Cook Islands-flagged tanker suspected of dragging its anchor and causing the damage. The vessel is linked to a “shadow fleet” transporting Russian oil despite sanctions. NATO announced increased presence in the Baltic Sea on December 27, while Russia dismissed the ship’s seizure. Finnish police later found seabed tracks pointing to Eagle S as the likely cause. A legal challenge by the ship’s UAE-based owner to release the vessel was rejected on January 3, 2025.
|
Subsea Cable Vulnerabilities Pose Growing Threat to Financial Stability
Recent incidents involving suspected sabotage of undersea data cables have raised alarms among governments and NATO, but an equally critical—yet overlooked—stakeholder is the global financial sector. Financial institutions in London and New York are highly dependent on the uninterrupted flow of data through over 500 undersea cables, which carry more than $10 trillion in transactions daily.
A 2023 incident involving a Russian-linked tanker damaging five cables in the Gulf of Finland illustrates the fragility of this infrastructure. While Finland has initiated rudimentary contingency plans for cable disruptions, most other nations—including financial giants like the U.S. and UK—lack such preparedness.
Subsea cables form the digital backbone of global finance. Despite having redundancy systems, multiple simultaneous disruptions could halt critical transactions, create market distortions, and jeopardize systemic stability. Recovery timelines are uncertain, and the financial liabilities in the event of halted multi-million-dollar transactions remain ambiguous.
Unlike cyberattacks or banking crises, for which structured response frameworks like the Bank of England’s SIMEX exercises, or the U.S. Sheltered Harbor exist, there is no clear protocol for managing extended cable outages. Planning must evolve to include financial authorities, governments, cable operators, insurers, and emergency repair teams.
The time to act is now—before a blackout turns from hypothetical to catastrophic.
Subsea Cables in the Asia-Pacific: Strategic Vulnerabilities and Resilience Gaps
The Asia-Pacific region sits at the heart of global digital infrastructure, hosting one of the highest concentrations of submarine cables. Yet this strategic advantage is accompanied by mounting vulnerabilities. Increasing geopolitical tension, slow repair protocols, and an overstretched maintenance fleet have exposed the Achilles’ heel of cyberspace in the region.
Cable disruptions are frequent and costly. In February 2022, Taiwan’s Matsu Islands were disconnected for 50 days after both of their undersea cables were severed—at least a third of such incidents in the area have been linked to Chinese vessels. While deliberate sabotage remains difficult to prove, the risk is amplified by fragile infrastructure and regional political sensitivities.
Despite a threefold expansion in the global cable network since 2010, investment in maintenance has not kept pace. Repair times now average 40 days, with the Asia-Pacific region facing the longest delays. Regulatory bottlenecks—such as Indonesia’s permit requirements—can add months to cable repair timelines. While ASEAN issued guidelines in 2019 to streamline approvals, implementation remains inconsistent. For example, Malaysia only updated its policies in mid-2024, and Indonesia continues to lag.
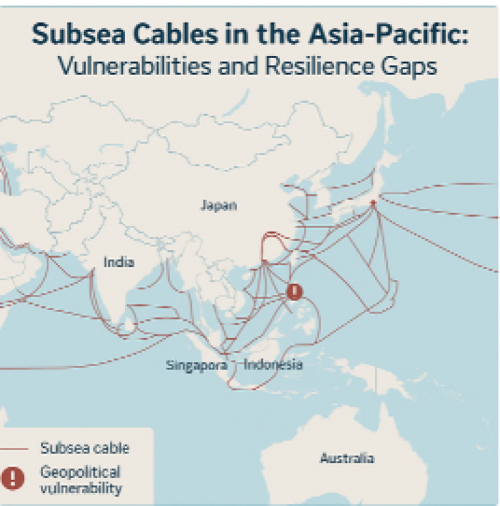
Cable redundancy varies sharply across the region. While countries like Australia, Japan, and Singapore benefit from multiple alternative routes, smaller island nations remain highly exposed. Tonga’s Vava’u islands endured 18 months of poor satellite connectivity after their sole cable was damaged in 2022.
Geopolitical competition further complicates resilience planning. Concerns over Chinese influence in cable ownership—particularly via firms like HMN Tech—have prompted the U.S., Japan, and Australia to push back through consortium restructuring and alternative infrastructure investments.
Although regional frameworks like SEAIOCMA provide some capacity for repair response, the limited number of repair-dedicated vessels (22 globally) and their aging condition constrain effectiveness. High costs—ranging from $600,000 to $3 million per cable repair—also raise concerns over equity, especially for smaller telecom operators serving remote communities.
As geopolitical and environmental risks escalate, the region must prioritize investment in cable redundancy, regulatory harmonization, and maintenance capacity. Multilateral efforts like the Quad Partnership for Cable Connectivity and Resilience offer promising pathways, but sustained public-private collaboration is essential to protect this critical—and increasingly contested—layer of the global digital economy.
Download the Full Report (pdf)